We live and work in a mobile-first, cloud-first world. But the cloud revolution hasn’t happened the way many people expected it to happen. Instead of organizations moving everything wholesale to the cloud in a “lift and shift” approach, it’s happened just like the introduction of every other “big new thing” over the last several decades: cloud technology has ended up being layered on top of what we’re already doing. So now we have desktop apps and SaaS apps and Web apps and mobile apps and cloud apps, and apps that defy categorization. (What is Office 365? Is it a desktop app? A cloud app? A mobile app? The answer is “D. All of the above.”)
Today’s workforce expects mobility. They expect to be able to use their own preferred mobile devices, not just whatever device happens to be the corporate standard issue. And the fact is that firewalls and similar security appliances, while still necessary, are no longer sufficient, because your corporate data is no longer confined to your corporate network – it’s out there on laptops, tablets, and smartphones, and on personal Dropbox accounts that your users set up when they got impatient and frustrated trying to do their jobs, and in Web and SaaS apps that users can potentially access from insecure locations and devices, such as Internet cafes, hotel business centers, the rent-a-computer at the local FedEx copy center, or Aunt Clara’s house.
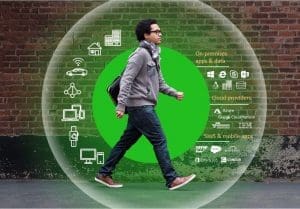
All of these forces are making it very difficult for organizations to strike the right balance between security and productivity. We don’t want to restrict mobility, because mobility has become a strategic business asset. It is essential to providing the kind of work/life balance that attracts the kind of employees we want to attract, and it is essential to achieve the business agility that comes from removing the barriers to when and where those employees can do their jobs. But to provide that mobility without compromising security, we have to re-think what our security perimeter looks like. We need a security perimeter that is user-centric rather than corporate network-centric.
That’s why people are talking about the concept of a secure mobile workspace. In fact, the term “Mobile Workspace” now has its own Wikipedia entry! And that’s why we partner with Citrix. Citrix has been a pioneer in secure, remote computing for over two decades, and remains at the leading edge of innovation in providing your organization with a secure mobile workspace – a single point of access that aggregates all of your apps and data, allows user access from any location using virtually any endpoint computing device, provides single sign-on, supports multi-factor authentication if you need it, and can sandbox your corporate apps and data away from the personal apps and data that a user may have on a personal mobile device. And if that device is lost or stolen, you can perform a remote factory reset to wipe it completely; or if the employee leaves the organization, the corporate apps and data can be remotely wiped without affecting personal apps and data.
And it gets even better because the whole environment can be wrapped in AI-driven analytics that not only monitors application performance but builds a baseline risk profile over time by observing how users typically interact with the environment. It can then spot anomalies in user behavior and automatically respond in a variety of ways: by alerting an administrator, by triggering session recording, by requiring a higher-than-normal level of user authentication, or by denying the connection altogether.
Performance and productivity vs. security is always a balancing act. But you really can provide users with the flexibility they need to work when and where they need to work while still maintaining the required level of security. We’d love to tell you more about how to do that.