Okay, I can’t believe we are still discussing this: Do not put your printers directly on the Internet!
These researchers make an excellent point supporting the previously mentioned assertion: printer software is not updated frequently enough to keep pace with attackers. A quick search on Shodan.io shows printers available online and accepting connections to TCP 9100, which the researchers used to gain access to the device(s).
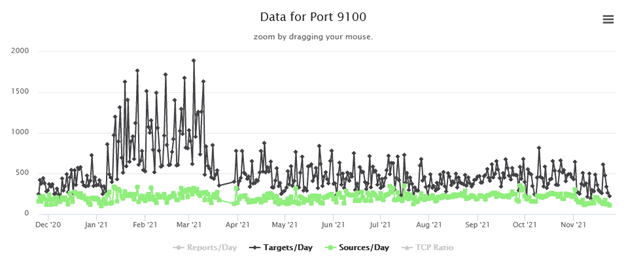
The SANS Internet Storm Center tracks these connections on the Internet, which shows that several hundred IP addresses are targeted every day.
However, let’s assume you have a justified business case to put a printer directly on the Internet and you have accepted the risk. How do you ensure attackers are not using that printer for nefarious purposes? You need to monitor the logs of the printer (however limited that may be), and you need to monitor the traffic to and from the printer. Build a baseline of what normal traffic looks like and alert on deviances of that traffic. Tools that will help you achieve this level of monitoring include a SIEM, network-based A/V, Sandbox, and an IPS. To ensure that your SOC analysts can focus on legitimate alerts, you should also back these tools with an ML and AI engine. Adding the ML/AI engine reduces false positives and can bring additional metadata, such as geo-location, known malicious IP addresses, associated botnets, and related malware to the attack type.